You’ve mastered the art of cloud infrastructure. You can provision resources, deploy applications, manage networks, and troubleshoot complex systems. But as you climb the ranks of cloud expertise, you encounter new challenges: How do you keep the most sensitive data—passwords and API keys—truly secure? How do you ensure your encryption keys are managed according to strict compliance rules? How do you quickly spin up a powerful command-line environment without any setup? And how do you leverage the cutting edge of artificial intelligence without becoming a machine learning expert yourself?
These are the tools and services in google cloud that empowering you with advanced security, enhanced productivity, and the magic of AI, all while adhering to best practices.
The Digital Strongbox: Secret Manager
In our journey, we’ve learned to avoid hardcoding sensitive information. We use ConfigMaps for non-sensitive data in Kubernetes, and we recommend avoiding storing passwords directly in code. But where do you really put that database password, that API key for a third-party service, or that TLS certificate?
You put it in Secret Manager.
Secret Manager is a fully managed, globally available service for securely storing, managing, and accessing secrets.
- Secure Storage: Secrets are stored encrypted at rest and in transit.
- Version Control: Every time you update a secret, Secret Manager creates a new version. This allows you to roll back to a previous version if needed.
- Auditing: It integrates with Cloud Audit Logs, so you always know who accessed which secret and when.
- Automatic Rotation: You can configure secrets to automatically rotate their values after a set period, further enhancing security.
- Access Control: Access to secrets is controlled via granular IAM permissions.
The Analogy: Imagine a highly secure, version-controlled safe in the cloud. Instead of writing your sensitive keys on sticky notes (or worse, in your code), you lock them away in this safe. Your applications, with the right digital key (IAM role), can then fetch the latest version of the secret when they need it, never needing to know the actual value beforehand.
Use Case: Your GKE application needs to connect to Cloud SQL. Instead of putting the database password in your container image, your application makes an API call to Secret Manager to retrieve the latest password at startup.
The Master Key Manager: Key Management Service (KMS)
You’re a responsible cloud engineer, so you know that data should always be encrypted, both at rest and in transit. Google Cloud encrypts customer data by default for many services. But for strict compliance requirements, you often need more control over the encryption keys themselves.
This is where Cloud Key Management Service (KMS) comes in.
KMS is a cloud-hosted key management service that lets you manage your cryptographic keys in a centralized, highly available, and globally consistent manner.
- Customer-Managed Encryption Keys (CMEK): With KMS, you create and manage your own encryption keys. You can then configure services like Cloud Storage, Persistent Disk, BigQuery, and even some databases to use your keys to encrypt your data. Google still handles the encryption/decryption process, but you control the key.
- Key Lifecycle Management: You manage the entire lifecycle of your keys: creation, rotation, enabling, disabling, and destruction.
- Hardware Security Modules (HSM): For the highest level of security, KMS offers the option to store your keys within FIPS 140-2 Level 3 validated Hardware Security Modules.
- Integration: It integrates with IAM for granular access control over who can use or administer your keys.
The Analogy: Think of KMS as your personal digital locksmith and key vault. Google automatically locks your data in various services, but with KMS, you get to own and manage the actual physical keys used for those locks. You can issue new keys, retire old ones, and dictate exactly who gets a copy.
Use Case: Your legal department requires that all data in your Cloud Storage buckets be encrypted with keys that your organization explicitly controls and rotates annually. You create a key in KMS, enable CMEK on your Cloud Storage bucket, and configure an annual key rotation policy.
Your Instant Command Center: Cloud Shell
You’re troubleshooting a critical issue on a GKE cluster. You need to run kubectl commands, check logs with gcloud logging, and maybe even spin up a quick VM with gcloud compute. Your laptop is acting up, or you’re on a public machine, or you simply don’t have all the tools installed locally. What do you do?
You launch Cloud Shell.
Cloud Shell is an interactive shell environment for Google Cloud, accessible directly from your web browser.
- Pre-configured Environment: It’s a temporary Compute Engine VM (running Debian Linux) that comes pre-loaded with almost every command-line tool you could possibly need:
gcloud,kubectl,terraform,ansible, Docker, various language SDKs (Node.js, Python, Java, Go), and more. - Always Authenticated: It’s automatically authenticated to your GCP account with your user credentials, and your current project is already set. No
gcloud auth loginneeded! - Persistent Home Directory: It includes 5 GB of persistent disk storage for your home directory, so your files, scripts, and configurations are saved between sessions.
- Integrated Editor: It includes a full-featured code editor (based on Monaco Editor) directly in the browser, allowing you to edit files without leaving Cloud Shell.
- Web Preview: You can expose web applications running in Cloud Shell on a temporary public port for testing.
The Analogy: Cloud Shell is like having a fully equipped, perfectly tuned, and always-ready cloud workstation available instantly, anywhere you have a web browser and an internet connection. It’s the ultimate productivity booster for GCP engineers.
Use Case: You need to quickly check the status of a Compute Engine instance from your tablet. You open the GCP Console, click the “Activate Cloud Shell” button, and within seconds, you’re typing gcloud compute instances list as if you were on your desktop machine.
The Software Store: Cloud Marketplace
You need to deploy a specific piece of third-party software—perhaps a popular database like MongoDB, a Content Management System like WordPress, or a monitoring tool like Grafana. You could manually set up a VM, install the OS, download the software, configure it, and secure it. This is a time-consuming and error-prone process.
Or you could use Cloud Marketplace.
Cloud Marketplace (formerly GCP Marketplace) is an online store that makes it easy to find, deploy, and manage third-party software and services that run on Google Cloud.
- One-Click Deployment: It offers pre-configured, optimized, and officially supported solutions for a wide range of software, ready to deploy with just a few clicks.
- Managed Solutions: Many offerings are fully managed services, not just VM images, simplifying operations.
- Billing Integration: The costs for Marketplace solutions are integrated directly into your Google Cloud bill, simplifying vendor management.
- Trusted Vendors: Solutions are vetted by Google, ensuring reliability and security.
The Analogy: Think of Cloud Marketplace as the Google Play Store or Apple App Store, but for enterprise software and cloud services. Instead of manually downloading and installing an app, you find what you need and deploy it directly into your GCP project, pre-configured and ready to run.
Use Case: Your marketing team needs a WordPress site. Instead of manually setting up a VM and installing WordPress, you find “WordPress” in Cloud Marketplace, configure a few options (like VM size and disk), and deploy a fully functional WordPress instance with a managed database in minutes.
The Smart Assistant: Google Cloud AI Services
Finally, let’s touch upon the magic of Artificial Intelligence. Google Cloud offers powerful, pre-trained AI services that you can integrate into your applications without writing complex ML models yourself. These are often called “API-first AI” or “AI Platform Services.”
- What they are: These are fully managed, consumption-based (pay-per-use) services that expose advanced AI capabilities through simple REST APIs. You send them data, and they return insights or transformations.
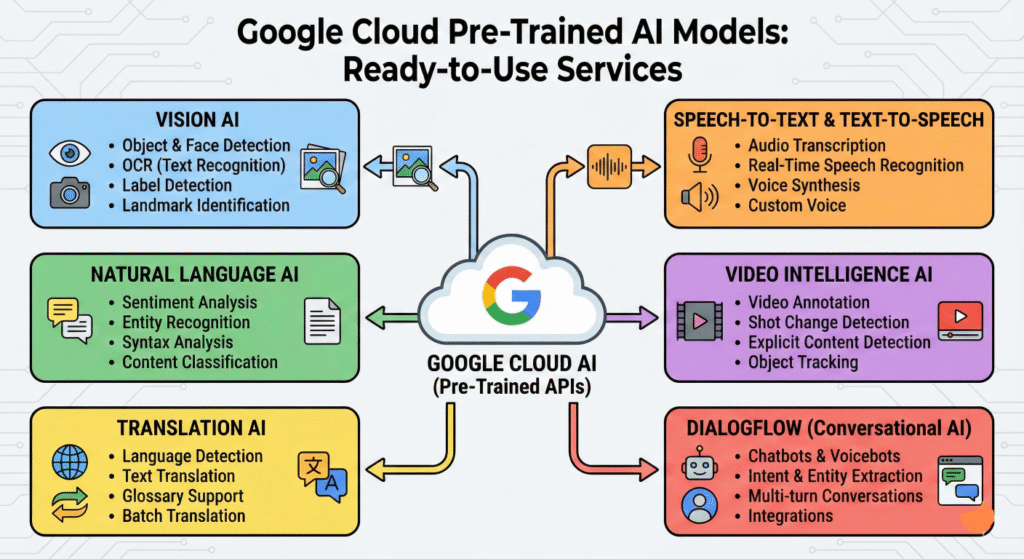
Here are a few key examples relevant to a general understanding:
- Cloud Vision AI: Allows applications to understand images.
- Analogy: It’s like giving your app eyes and a brain.
- Use Case: You upload an image to a Cloud Storage bucket, and a Cloud Function triggers Vision AI. It can detect objects (e.g., “This image contains a car, a tree, a person”), recognize text (OCR), detect faces, or identify explicit content.
- Cloud Natural Language AI: Helps applications understand text.
- Analogy: It gives your app the ability to read and comprehend.
- Use Case: Analyze customer reviews from your App Engine application to determine sentiment (positive, negative, neutral), extract entities (people, places, organizations), or classify content into categories.
- Cloud Translation AI: Translates text between languages.
- Analogy: Your app gains a universal translator.
- Use Case: Translate user input or dynamically serve website content in multiple languages from your Cloud Run service.
- Cloud Speech-to-Text & Text-to-Speech: Convert audio to text and text to lifelike speech.
- Analogy: Your app can hear and speak.
- Use Case: Transcribe customer service calls (Speech-to-Text) or power voice interfaces for your applications (Text-to-Speech).
The Takeaway: understand that Google Cloud provides these ready-to-use AI services. You don’t build the models; you just send your data to an API, and Google’s pre-trained models do the heavy lifting.
Common Pitfalls & Best Practices
- Secret Manager:
- Pitfall: Giving too broad an IAM role (e.g.,
Secret Manager Admin) to an application that only needs to read a secret. - Best Practice: Use the principle of least privilege: grant only the
Secret Manager Secret Accessor(roles/secretmanager.secretAccessor) role to applications.
- Pitfall: Giving too broad an IAM role (e.g.,
- KMS:
- Pitfall: Confusing default encryption (Google-managed keys) with CMEK.
- Best Practice: Understand that CMEK is for when your organization needs to control the keys, often for compliance. Default encryption is usually sufficient otherwise.
- Cloud Shell:
- Pitfall: Storing highly sensitive, unencrypted data in your Cloud Shell home directory.
- Best Practice: Treat your Cloud Shell as a working environment, not a permanent storage location for sensitive data. Use Secret Manager for secrets.
- Cloud Marketplace:
- Pitfall: Deploying Marketplace solutions without reviewing their underlying resources and billing implications.
- Best Practice: Always understand what resources a Marketplace solution will deploy and how it will be billed before deploying to production.
- AI Services:
- Pitfall: Trying to use a pre-trained API-first AI service for a highly specialized, niche problem (e.g., identifying a specific rare type of mold in images).
- Best Practice: Use API-first AI for common, well-defined tasks (sentiment, object detection). For highly specialized tasks, you might need custom ML models (which is beyond the ACE exam scope).
Quick Reference Command Center
| Service | Action | Command |
|---|---|---|
| Secret Manager | Create a Secret | gcloud secrets create [SECRET_NAME] --data-file=my-secret.txt |
| Secret Manager | Access a Secret | gcloud secrets versions access latest --secret=[SECRET_NAME] |
| KMS | Create a Key Ring | gcloud kms keyrings create [KEY_RING_NAME] --location=[REGION] |
| KMS | Create a Key | gcloud kms keys create [KEY_NAME] --keyring=[KEY_RING_NAME] --location=[REGION] --purpose=encryption |
| Cloud Shell | Launch Cloud Shell | (Click “Activate Cloud Shell” in Console) |
| Cloud Shell | Open Editor | cloudshell edit . |
| Cloud Marketplace | Browse Marketplace | (Navigate to Marketplace in Console) |
| Cloud Vision AI | Detect Labels in Image | gcloud ml vision detect-labels gs://[BUCKET]/image.jpg |

